by Dmitry Kirsanov
15. May 2019 01:08
We have seen it often, with almost every known social network and platform built to express yourself - at some point it gets to a milestone which changes the platform to the opposite of its original vision.
"Don't be evil" becomes THE evil, the outlaw becomes the law enforcer, independent form alliances and neutral become ferocious fighters against neutrality. There are still islands of free speech, where borders are wide enough to call it unbiased, but they are doing it with serious personal risk and at significant expenses.
In this essay I'll try to analyse the history, trends and risks of self-expression platforms, and provide some food for thought for those who will attempt to build the next platform.
The most important aspect of this work is technology, second is sociology and third - economy. We'll scrape the law a bit, but the main premise will be that whatever you are doing is illegal somewhere, and if not - then content certainly will be. And so we'll use technology to obey the law when possible, and protect from it when it's not.
But first - let's look at existing platforms and their pitfalls. This will help us to list the known problems and caveats, and see how titans fell and why. More...
by Dmitry Kirsanov
30. April 2019 11:28
Recently I analysed logs of some of my mobile apps, mostly enterprise with backend web services. And some thoughts that result from it are well worth sharing. That mainly concerns architects and developers of corporate apps, rather than game or standalone apps – network-related problems are harder to solve, as you don’t control the environment.
More...
by Dmitry Kirsanov
7. March 2019 12:44
I think every system administrator is doing this often enough to think about automating it. When you make changes to file, deploy a new version and not sure if you’ll need to revert, and there is a number of previous copies that you would like to keep track of.
This little command line utility does exactly that – it creates the .bak file for whatever file, maintains any number of older backups (.bak1, .bak2 and so on), restores from .bak (this will also rename .bak2 to .bak1 and all older versions too), deletes all backups if needed, and can also keep backups in different directory – for cases when you are modifying file in publicly available directory or just don’t like clutter.
Get more information and binary on utility page
by Dmitry Kirsanov
15. February 2019 14:04
Here is a small utility I made to facilitate integrations, log and backup shipping between servers, but would love to have it years ago. A command-line ftp uploader. I’ll add some additional features to it, though it already covers all bases for me.
Available here.
If the link above doesn’t work, just take a look at “Side Projects” link at the bottom of right column.
by Dmitry Kirsanov
7. February 2019 11:27
One of the most hated parts of Google Chrome is it's Software Reporter Tool. This executable file is started by Chrome and supposedly is providing Google with logs from your computer. Either way, it's the fastest way to drain your laptop battery, make computer stutter and noisy. People often ask about the way to get rid of this software reporter tool, but the best advice they get is to modify the security permissions on executable file. Basically, the most common advice is to open the file settings, go to Security tab, ensure the security settings are not propagated from parent (in this case - directory) and then remove all access rights, making this file non-readable. Well, it only works till the next time Google Chrome updates.
A bit better way to lock this (or any other annoying) executable file is by using your Windows Group Policies. More...
by Dmitry Kirsanov
21. March 2018 08:25
Alright, here is a bit embarrassing release, because this application is just 45 lines long. That’s including blank ones. This little tool is for using in batch (.bat or .cmd) files so that you could wait X seconds between issuing commands. It’s printing the countdown and then exits.
I would like to thank Microsoft for making this lifetime project possible. Without them it wouldn’t be.
Usage:
wait.exe [X]
where X is number of seconds to wait, e.g. wait 5
The app is compiled for .NET Framework 4 Client Profile, so it’s compatible with Windows XP and up. Zip file contains both binary and source file.
Note:
If you are using Windows 7 or up, you can simply type “timeout 5” in your batch file to wait 4-5 seconds. Yes, it’s not as precise as this amazing tool, but do we really need it to be? In Windows XP, there is no timeout alternative, so using of this tool is reasonable.
More...
by Dmitry Kirsanov
15. March 2018 18:58
The Why
Like a pro system administrator, I have to reset and generate passwords. A few per day. They are for different purposes and of different kind – PINs, short passwords, long password, the ones for web services, terminals, windows users – you name it.
Previously, to generate the password I was using Password Safe – the password managing utility originally made by Bruce Schneier. Everything was more or less fine, but in order to use specific policy (or set of rules) I would have to open my password safe, and I would prefer not to.
I wanted to have more flexible tool, fast and compact, that would do everything I want and then some more. Eventually I’ve got a few hours to invest into it.
The What
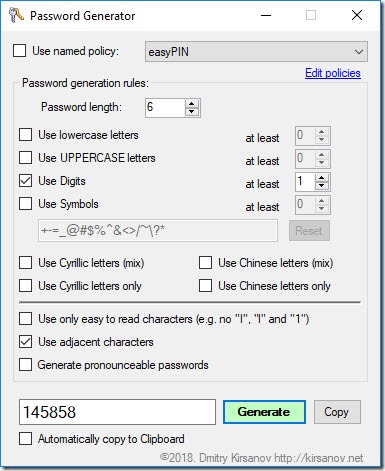
I copied the UI of password generation dialogue from Password Safe, as it’s both ergonomic and habitual. And then I added few elements which made this app unique and, let’s be honest, better tool.
The new features are:
- Ability to add Cyrillic (Russian) and Chinese (Simplified) characters – either as an addition (mix) or replacement to English alphabet.
- Use adjacent characters on standard QWERTY keyboard.
- Automatically copy generated passwords to clipboard.
- Some tweaks to how passwords are generated.
More...
by Dmitry Kirsanov
9. April 2017 02:55
 Just recently I had to assign a new virtual machine for yet another project, and this presented a perfect opportunity to try the recently introduced feature of Azure storage – the SSD drives.
Just recently I had to assign a new virtual machine for yet another project, and this presented a perfect opportunity to try the recently introduced feature of Azure storage – the SSD drives.
As you know (and if you don’t – you can read about it here), the type of memory used in SSD drives provides not only faster way to write and read data, but more importantly – to read non-sequential data, hence promising a better performance for database and web caching. But, of course, I had to test it before putting any eggs into that basket.
One thing that raised some suspicion was the IOPS limit mentioned in each virtual machine “size” chart. The “size” of virtual machine, in Azure jargon, is the specs. Usually the name of the “size” consists of the literal and a cipher. The first tells us about the purpose of the machine and the second – how powerful and expensive it is.
I’ve selected the virtual machine that had “SSD 7Gb” on it, wondering what it means. Turned out that it means that you’ll get the temporary drive (the one with contents wiped time after time) with total size of 7Gb, but part of it will be taken by the virtual memory file. Still, you’ll get over 5Gb left and I never needed even that much on a temporary drive. More...
by Dmitry Kirsanov
9. April 2017 00:16
 A lesson for mobile developers.
A lesson for mobile developers.
When you steal from IT corporation, it’s a theft. When corporation steals from you – it’s a progress.
You may live through an event in your life, when stars align and you discover a new niche, where you would be a pioneer. Get the moment of enlightenment, hectically lookup the Internet for solutions and be amazed that no one else did that. You would actually be the first. And there is no guarantee, that it will be success – in a heap of millions of apps and websites and info-noise of events, things are missed. In Android alone, there are 2.8 millions of apps today, and it’s still growing.
Indie projects are akin to live creatures – born in a coincidence that looks like a miracle, they start small and weak, just like most creatures on our planet – and they don’t look like what they will in a few months from now. At that time they are easiest to snatch by all sorts of predators and the nature.
How much it costs to make an app
I calculated, that getting one new user for a mobile app will cost you around More...
by Dmitry Kirsanov
28. November 2016 11:33
It finally happened. My first app for Android platform is just about to be released and is available in Beta channel. It was clear that I’m not going to release anything for Windows Phone market anymore, especially since all phones in family are Android based, but I had to start somewhere in Android, and what a start it is!
The idea came during the Halloween night, when I was about to pick up the trick-or-treaters and their parents from neighbourhood. The problem was – it was night, I didn’t know where they are at the moment, and they were wandering among other spooky wanderers. I needed to know their location, precise and fresh. It took a few phone calls and messages with coordinates until I found them. Not a big problem, but I would rather get rid of that.
Second problem was recurrent – when I have to pick up someone using the car, I want to make sure that person knows my whereabouts, so neither of us would have to wait. Or when I want to show where I am, so family would know when to expect me. And that I’m fine and where I am supposed to be.
And a nuance – I never want this information to be available all the time. For various reasons – from privacy to battery life of my phone. I want to press the button, share my location, and for a limited time I want that location to be current. More...